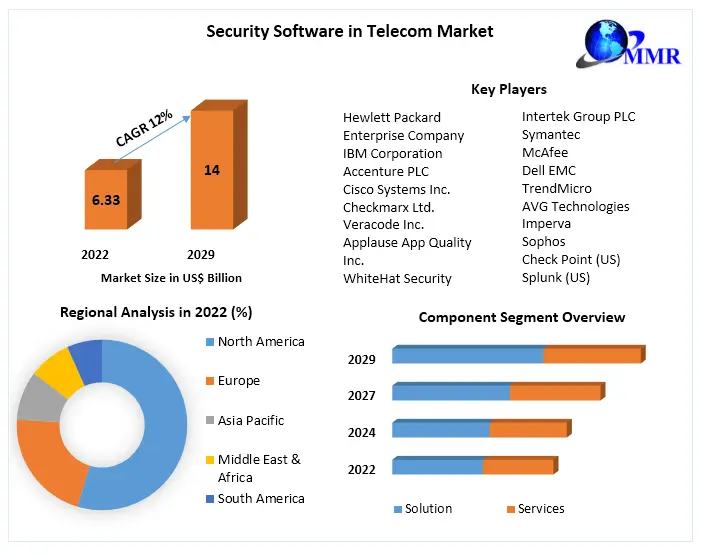
Global Security Software in Telecom Market
Table of Content
1. Preface
1.1. Report Scope and Market Segmentation
1.2. Research Highlights
1.3. Research Objectives
2. Assumptions and Research Methodology
2.1. Report Assumptions
2.2. Abbreviations
2.3. Research Methodology
2.3.1. Secondary Research
2.3.1.1. Secondary data
2.3.1.2. Secondary Sources
2.3.2. Primary Research
2.3.2.1. Data from Primary Sources
2.3.2.2. Breakdown of Primary Sources
3. Executive Summary: Global Security Software in Telecom Market Size, by Market Value (US$ Bn)
4. Market Overview
4.1. Introduction
4.2. Market Indicator
4.2.1. Drivers
4.2.2. Restraints
4.2.3. Opportunities
4.2.4. Challenges
4.3. Porter’s Analysis
4.4. Value Chain Analysis
4.5. Market Risk Analysis
4.6. SWOT Analysis
4.7. Industry Trends and Emerging Technologies
5. Supply Side and Demand Side Indicators
6. Global Security Software in Telecom Market Analysis and Forecast
6.1. Global Security Software in Telecom Market Size & Y-o-Y Growth Analysis
6.1.1. North America
6.1.2. Europe
6.1.3. Asia Pacific
6.1.4. Middle East & Africa
6.1.5. South America
7. Global Security Software in Telecom Market Analysis and Forecast, by Component
7.1. Introduction and Definition
7.2. Key Findings
7.3. Global Security Software in Telecom Market Value Share Analysis, by Component
7.4. Global Security Software in Telecom Market Size (US$ Bn) Forecast, by Component
7.5. Global Security Software in Telecom Market Analysis, by Component
7.6. Global Security Software in Telecom Market Attractiveness Analysis, by Component
8. Global Security Software in Telecom Market Analysis and Forecast, by Security Type
8.1. Introduction and Definition
8.2. Key Findings
8.3. Global Security Software in Telecom Market Value Share Analysis, by Security Type
8.4. Global Security Software in Telecom Market Size (US$ Bn) Forecast, by Security Type
8.5. Global Security Software in Telecom Market Analysis, by Security Type
8.6. Global Security Software in Telecom Market Attractiveness Analysis, by Security Type
9. Global Security Software in Telecom Market Analysis and Forecast, by Deployment Type
9.1. Introduction and Definition
9.2. Key Findings
9.3. Global Security Software in Telecom Market Value Share Analysis, by Deployment Type
9.4. Global Security Software in Telecom Market Size (US$ Bn) Forecast, by Deployment Type
9.5. Global Security Software in Telecom Market Analysis, by Deployment Type
9.6. Global Security Software in Telecom Market Attractiveness Analysis, by Deployment Type
10. Global Security Software in Telecom Market Analysis and Forecast, by Applications
10.1. Introduction and Definition
10.2. Key Findings
10.3. Global Security Software in Telecom Market Value Share Analysis, by Applications
10.4. Global Security Software in Telecom Market Size (US$ Bn) Forecast, by Applications
10.5. Global Security Software in Telecom Market Analysis, by Applications
10.6. Global Security Software in Telecom Market Attractiveness Analysis, by Applications
11. Global Security Software in Telecom Market Analysis, by Region
11.1. Global Security Software in Telecom Market Value Share Analysis, by Region
11.2. Global Security Software in Telecom Market Size (US$ Bn) Forecast, by Region
11.3. Global Security Software in Telecom Market Attractiveness Analysis, by Region
12. North America Security Software in Telecom Market Analysis
12.1. Key Findings
12.2. North America Security Software in Telecom Market Overview
12.3. North America Security Software in Telecom Market Value Share Analysis, by Component
12.4. North America Security Software in Telecom Market Forecast, by Component
12.4.1. Solution
12.4.2. Services
12.5. North America Security Software in Telecom Market Value Share Analysis, by Security Type
12.6. North America Security Software in Telecom Market Forecast, by Security Type
12.6.1. Network Security
12.6.2. Endpoint Security
12.6.3. Application Security
12.6.4. Cloud Security
12.6.5. Others
12.7. North America Security Software in Telecom Market Value Share Analysis, by Deployment Type
12.8. North America Security Software in Telecom Market Forecast, by Deployment Type
12.8.1. Cloud-Based
12.8.2. On-Premise
12.9. North America Security Software in Telecom Market Value Share Analysis, by Applications
12.10. North America Security Software in Telecom Market Forecast, by Applications
12.10.1. Small and Medium Enterprises (SMEs)
12.10.2. Large Enterprises
12.10.3. Government Organizations
12.11. North America Security Software in Telecom Market Value Share Analysis, by Country
12.12. North America Security Software in Telecom Market Forecast, by Country
12.12.1. U.S.
12.12.2. Canada
12.13. North America Security Software in Telecom Market Analysis, by Country
12.14. U.S. Security Software in Telecom Market Forecast, by Component
12.14.1. Solution
12.14.2. Services
12.15. U.S. Security Software in Telecom Market Forecast, by Security Type
12.15.1. Network Security
12.15.2. Endpoint Security
12.15.3. Application Security
12.15.4. Cloud Security
12.15.5. Others
12.16. U.S. Security Software in Telecom Market Forecast, by Deployment Type
12.16.1. Cloud-Based
12.16.2. On-Premise
12.17. U.S. Security Software in Telecom Market Forecast, by Applications
12.17.1. Small and Medium Enterprises (SMEs)
12.17.2. Large Enterprises
12.17.3. Government Organizations
12.18. Canada Security Software in Telecom Market Forecast, by Component
12.18.1. Solution
12.18.2. Services
12.19. Canada Security Software in Telecom Market Forecast, by Security Type
12.19.1. Network Security
12.19.2. Endpoint Security
12.19.3. Application Security
12.19.4. Cloud Security
12.19.5. Others
12.20. Canada Security Software in Telecom Market Forecast, by Deployment Type
12.20.1. Cloud-Based
12.20.2. On-Premise
12.21. Canada Security Software in Telecom Market Forecast, by Applications
12.21.1. Small and Medium Enterprises (SMEs)
12.21.2. Large Enterprises
12.21.3. Government Organizations
12.22. North America Security Software in Telecom Market Attractiveness Analysis
12.22.1. By Component
12.22.2. By Security Type
12.22.3. By Deployment Type
12.22.4. By Applications
12.23. PEST Analysis
12.24. Key Trends
12.25. Key Developments
13. Europe Security Software in Telecom Market Analysis
13.1. Key Findings
13.2. Europe Security Software in Telecom Market Overview
13.3. Europe Security Software in Telecom Market Value Share Analysis, by Component
13.4. Europe Security Software in Telecom Market Forecast, by Component
13.4.1. Solution
13.4.2. Services
13.5. Europe Security Software in Telecom Market Value Share Analysis, by Security Type
13.6. Europe Security Software in Telecom Market Forecast, by Security Type
13.6.1. Network Security
13.6.2. Endpoint Security
13.6.3. Application Security
13.6.4. Cloud Security
13.6.5. Others
13.7. Europe Security Software in Telecom Market Value Share Analysis, by Deployment Type
13.8. Europe Security Software in Telecom Market Forecast, by Deployment Type
13.8.1. Cloud-Based
13.8.2. On-Premise
13.9. Europe Security Software in Telecom Market Value Share Analysis, by Applications
13.10. Europe Security Software in Telecom Market Forecast, by Applications
13.10.1. Small and Medium Enterprises (SMEs)
13.10.2. Large Enterprises
13.10.3. Government Organizations
13.11. Europe Security Software in Telecom Market Value Share Analysis, by Country
13.12. Europe Security Software in Telecom Market Forecast, by Country
13.12.1. Germany
13.12.2. U.K.
13.12.3. France
13.12.4. Italy
13.12.5. Spain
13.12.6. Rest of Europe
13.13. Europe Security Software in Telecom Market Analysis, by Country
13.14. Germany Security Software in Telecom Market Forecast, by Component
13.14.1. Solution
13.14.2. Services
13.15. Germany Security Software in Telecom Market Forecast, by Security Type
13.15.1. Network Security
13.15.2. Endpoint Security
13.15.3. Application Security
13.15.4. Cloud Security
13.15.5. Others
13.16. Germany Security Software in Telecom Market Forecast, by Deployment Type
13.16.1. Cloud-Based
13.16.2. On-Premise
13.17. Germany Security Software in Telecom Market Forecast, by Applications
13.17.1. Small and Medium Enterprises (SMEs)
13.17.2. Large Enterprises
13.17.3. Government Organizations
13.18. U.K. Security Software in Telecom Market Forecast, by Component
13.18.1. Solution
13.18.2. Services
13.19. U.K. Security Software in Telecom Market Forecast, by Security Type
13.19.1. Network Security
13.19.2. Endpoint Security
13.19.3. Application Security
13.19.4. Cloud Security
13.19.5. Others
13.20. U.K. Security Software in Telecom Market Forecast, by Deployment Type
13.20.1. Cloud-Based
13.20.2. On-Premise
13.21. U.K. Security Software in Telecom Market Forecast, by Applications
13.21.1. Small and Medium Enterprises (SMEs)
13.21.2. Large Enterprises
13.21.3. Government Organizations
13.22. France Security Software in Telecom Market Forecast, by Component
13.22.1. Solution
13.22.2. Services
13.23. France Security Software in Telecom Market Forecast, by Security Type
13.23.1. Network Security
13.23.2. Endpoint Security
13.23.3. Application Security
13.23.4. Cloud Security
13.23.5. Others
13.24. France Security Software in Telecom Market Forecast, by Deployment Type
13.24.1. Cloud-Based
13.24.2. On-Premise
13.25. France Security Software in Telecom Market Forecast, by Applications
13.25.1. Small and Medium Enterprises (SMEs)
13.25.2. Large Enterprises
13.25.3. Government Organizations
13.26. Italy Security Software in Telecom Market Forecast, by Component
13.26.1. Solution
13.26.2. Services
13.27. Italy Security Software in Telecom Market Forecast, by Security Type
13.27.1. Network Security
13.27.2. Endpoint Security
13.27.3. Application Security
13.27.4. Cloud Security
13.27.5. Others
13.28. Italy Security Software in Telecom Market Forecast, by Deployment Type
13.28.1. Cloud-Based
13.28.2. On-Premise
13.29. Italy Security Software in Telecom Market Forecast, by Applications
13.29.1. Small and Medium Enterprises (SMEs)
13.29.2. Large Enterprises
13.29.3. Government Organizations
13.30. Spain Security Software in Telecom Market Forecast, by Component
13.30.1. Solution
13.30.2. Services
13.31. Spain Security Software in Telecom Market Forecast, by Security Type
13.31.1. Network Security
13.31.2. Endpoint Security
13.31.3. Application Security
13.31.4. Cloud Security
13.31.5. Others
13.32. Spain Security Software in Telecom Market Forecast, by Deployment Type
13.32.1. Cloud-Based
13.32.2. On-Premise
13.33. Spain Security Software in Telecom Market Forecast, by Applications
13.33.1. Small and Medium Enterprises (SMEs)
13.33.2. Large Enterprises
13.33.3. Government Organizations
13.34. Rest of Europe Security Software in Telecom Market Forecast, by Component
13.34.1. Solution
13.34.2. Services
13.35. Rest of Europe Security Software in Telecom Market Forecast, by Security Type
13.35.1. Network Security
13.35.2. Endpoint Security
13.35.3. Application Security
13.35.4. Cloud Security
13.35.5. Others
13.36. Rest of Europe Security Software in Telecom Market Forecast, by Deployment Type
13.36.1. Cloud-Based
13.36.2. On-Premise
13.37. Rest Of Europe Security Software in Telecom Market Forecast, by Applications
13.37.1. Small and Medium Enterprises (SMEs)
13.37.2. Large Enterprises
13.37.3. Government Organizations
13.38. Europe Security Software in Telecom Market Attractiveness Analysis
13.38.1. By Component
13.38.2. By Security Type
13.38.3. By Deployment Type
13.38.4. By Applications
13.39. PEST Analysis
13.40. Key Trends
13.41. Key Developments
14. Asia Pacific Security Software in Telecom Market Analysis
14.1. Key Findings
14.2. Asia Pacific Security Software in Telecom Market Overview
14.3. Asia Pacific Security Software in Telecom Market Value Share Analysis, by Component
14.4. Asia Pacific Security Software in Telecom Market Forecast, by Component
14.4.1. Solution
14.4.2. Services
14.5. Asia Pacific Security Software in Telecom Market Value Share Analysis, by Security Type
14.6. Asia Pacific Security Software in Telecom Market Forecast, by Security Type
14.6.1. Network Security
14.6.2. Endpoint Security
14.6.3. Application Security
14.6.4. Cloud Security
14.6.5. Others
14.7. Asia Pacific Security Software in Telecom Market Value Share Analysis, by Deployment Type
14.8. Asia Pacific Security Software in Telecom Market Forecast, by Deployment Type
14.8.1. Cloud-Based
14.8.2. On-Premise
14.9. Asia Pacific Security Software in Telecom Market Value Share Analysis, by Applications
14.10. Asia Pacific Security Software in Telecom Market Forecast, by Applications
14.10.1. Small and Medium Enterprises (SMEs)
14.10.2. Large Enterprises
14.10.3. Government Organizations
14.11. Asia Pacific Security Software in Telecom Market Value Share Analysis, by Country
14.12. Asia Pacific Security Software in Telecom Market Forecast, by Country
14.12.1. China
14.12.2. India
14.12.3. Japan
14.12.4. ASEAN
14.12.5. Rest of Asia Pacific
14.13. Asia Pacific Security Software in Telecom Market Analysis, by Country
14.14. China Security Software in Telecom Market Forecast, by Component
14.14.1. Solution
14.14.2. Services
14.15. China Security Software in Telecom Market Forecast, by Security Type
14.15.1. Network Security
14.15.2. Endpoint Security
14.15.3. Application Security
14.15.4. Cloud Security
14.15.5. Others
14.16. China Security Software in Telecom Market Forecast, by Deployment Type
14.16.1. Cloud-Based
14.16.2. On-Premise
14.17. China Security Software in Telecom Market Forecast, by Applications
14.17.1. Small and Medium Enterprises (SMEs)
14.17.2. Large Enterprises
14.17.3. Government Organizations
14.18. India Security Software in Telecom Market Forecast, by Component
14.18.1. Solution
14.18.2. Services
14.19. India Security Software in Telecom Market Forecast, by Security Type
14.19.1. Network Security
14.19.2. Endpoint Security
14.19.3. Application Security
14.19.4. Cloud Security
14.19.5. Others
14.20. India Security Software in Telecom Market Forecast, by Deployment Type
14.20.1. Cloud-Based
14.20.2. On-Premise
14.21. India Security Software in Telecom Market Forecast, by Applications
14.21.1. Small and Medium Enterprises (SMEs)
14.21.2. Large Enterprises
14.21.3. Government Organizations
14.22. Japan Security Software in Telecom Market Forecast, by Component
14.22.1. Solution
14.22.2. Services
14.23. Japan Security Software in Telecom Market Forecast, by Security Type
14.23.1. Network Security
14.23.2. Endpoint Security
14.23.3. Application Security
14.23.4. Cloud Security
14.23.5. Others
14.24. Japan Security Software in Telecom Market Forecast, by Deployment Type
14.24.1. Cloud-Based
14.24.2. On-Premise
14.25. Japan Security Software in Telecom Market Forecast, by Applications
14.25.1. Small and Medium Enterprises (SMEs)
14.25.2. Large Enterprises
14.25.3. Government Organizations
14.26. ASEAN Security Software in Telecom Market Forecast, by Component
14.26.1. Solution
14.26.2. Services
14.27. ASEAN Security Software in Telecom Market Forecast, by Security Type
14.27.1. Network Security
14.27.2. Endpoint Security
14.27.3. Application Security
14.27.4. Cloud Security
14.27.5. Others
14.28. ASEAN Security Software in Telecom Market Forecast, by Deployment Type
14.28.1. Cloud-Based
14.28.2. On-Premise
14.29. ASEAN Security Software in Telecom Market Forecast, by Applications
14.29.1. Small and Medium Enterprises (SMEs)
14.29.2. Large Enterprises
14.29.3. Government Organizations
14.30. Rest of Asia Pacific Security Software in Telecom Market Forecast, by Component
14.30.1. Solution
14.30.2. Services
14.31. Rest of Asia Pacific Security Software in Telecom Market Forecast, by Security Type
14.31.1. Network Security
14.31.2. Endpoint Security
14.31.3. Application Security
14.31.4. Cloud Security
14.31.5. Others
14.32. Rest of Asia Pacific Security Software in Telecom Market Forecast, by Deployment Type
14.32.1. Cloud-Based
14.32.2. On-Premise
14.33. Rest of Asia Pacific Security Software in Telecom Market Forecast, by Applications
14.33.1. Small and Medium Enterprises (SMEs)
14.33.2. Large Enterprises
14.33.3. Government Organizations
14.34. Asia Pacific Security Software in Telecom Market Attractiveness Analysis
14.34.1. By Component
14.34.2. By Security Type
14.34.3. By Deployment Type
14.34.4. By Applications
14.35. PEST Analysis
14.36. Key Trends
14.37. Key Developments
15. Middle East & Africa Security Software in Telecom Market Analysis
15.1. Key Findings
15.2. Middle East & Africa Security Software in Telecom Market Overview
15.3. Middle East & Africa Security Software in Telecom Market Value Share Analysis, by Component
15.4. Middle East & Africa Security Software in Telecom Market Forecast, by Component
15.4.1. Solution
15.4.2. Services
15.5. Middle East & Africa Security Software in Telecom Market Value Share Analysis, by Security Type
15.6. Middle East & Africa Security Software in Telecom Market Forecast, by Security Type
15.6.1. Network Security
15.6.2. Endpoint Security
15.6.3. Application Security
15.6.4. Cloud Security
15.6.5. Others
15.7. Middle East & Africa Security Software in Telecom Market Value Share Analysis, by Deployment Type
15.8. Middle East & Africa Security Software in Telecom Market Forecast, by Deployment Type
15.8.1. Cloud-Based
15.8.2. On-Premise
15.9. Middle East & Africa Security Software in Telecom Market Value Share Analysis, by Applications
15.10. Middle East & Africa Security Software in Telecom Market Forecast, by Applications
15.10.1. Small and Medium Enterprises (SMEs)
15.10.2. Large Enterprises
15.10.3. Government Organizations
15.11. Middle East & Africa Security Software in Telecom Market Value Share Analysis, by Country
15.12. Middle East & Africa Security Software in Telecom Market Forecast, by Country
15.12.1. GCC
15.12.2. South Africa
15.12.3. Rest of Middle East & Africa
15.13. Middle East & Africa Security Software in Telecom Market Analysis, by Country
15.14. GCC Security Software in Telecom Market Forecast, by Component
15.14.1. Solution
15.14.2. Services
15.15. GCC Security Software in Telecom Market Forecast, by Security Type
15.15.1. Network Security
15.15.2. Endpoint Security
15.15.3. Application Security
15.15.4. Cloud Security
15.15.5. Others
15.16. GCC Security Software in Telecom Market Forecast, by Deployment Type
15.16.1. Cloud-Based
15.16.2. On-Premise
15.17. GCC Security Software in Telecom Market Forecast, by Applications
15.17.1. Small and Medium Enterprises (SMEs)
15.17.2. Large Enterprises
15.17.3. Government Organizations
15.18. South Africa Security Software in Telecom Market Forecast, by Component
15.18.1. Solution
15.18.2. Services
15.19. South Africa Security Software in Telecom Market Forecast, by Security Type
15.19.1. Network Security
15.19.2. Endpoint Security
15.19.3. Application Security
15.19.4. Cloud Security
15.19.5. Others
15.20. South Africa Security Software in Telecom Market Forecast, by Deployment Type
15.20.1. Cloud-Based
15.20.2. On-Premise
15.21. South Africa Security Software in Telecom Market Forecast, by Applications
15.21.1. Small and Medium Enterprises (SMEs)
15.21.2. Large Enterprises
15.21.3. Government Organizations
15.22. Rest of Middle East & Africa Security Software in Telecom Market Forecast, by Component
15.22.1. Solution
15.22.2. Services
15.23. Rest of Middle East & Africa Security Software in Telecom Market Forecast, by Security Type
15.23.1. Network Security
15.23.2. Endpoint Security
15.23.3. Application Security
15.23.4. Cloud Security
15.23.5. Others
15.24. Rest of Middle East & Africa Security Software in Telecom Market Forecast, by Deployment Type
15.24.1. Cloud-Based
15.24.2. On-Premise
15.25. Rest of Middle East & Africa Security Software in Telecom Market Forecast, by Applications
15.25.1. Small and Medium Enterprises (SMEs)
15.25.2. Large Enterprises
15.25.3. Government Organizations
15.26. Middle East & Africa Security Software in Telecom Market Attractiveness Analysis
15.26.1. By Component
15.26.2. By Security Type
15.26.3. By Deployment Type
15.26.4. By Applications
15.27. PEST Analysis
15.28. Key Trends
15.29. Key Developments
16. South America Security Software in Telecom Market Analysis
16.1. Key Findings
16.2. South America Security Software in Telecom Market Overview
16.3. South America Security Software in Telecom Market Value Share Analysis, by Component
16.4. South America Security Software in Telecom Market Forecast, by Component
16.4.1. Solution
16.4.2. Services
16.5. South America Security Software in Telecom Market Value Share Analysis, by Security Type
16.6. South America Security Software in Telecom Market Forecast, by Security Type
16.6.1. Network Security
16.6.2. Endpoint Security
16.6.3. Application Security
16.6.4. Cloud Security
16.6.5. Others
16.7. South America Security Software in Telecom Market Value Share Analysis, by Deployment Type
16.8. South America Security Software in Telecom Market Forecast, by Deployment Type
16.8.1. Cloud-Based
16.8.2. On-Premise
16.9. South America Security Software in Telecom Market Value Share Analysis, by Applications
16.10. South America Security Software in Telecom Market Forecast, by Applications
16.10.1. Small and Medium Enterprises (SMEs)
16.10.2. Large Enterprises
16.10.3. Government Organizations
16.11. South America Security Software in Telecom Market Value Share Analysis, by Country
16.12. South America Security Software in Telecom Market Forecast, by Country
16.12.1. Brazil
16.12.2. Mexico
16.12.3. Rest of South America
16.13. South America Security Software in Telecom Market Analysis, by Country
16.14. Brazil Security Software in Telecom Market Forecast, by Component
16.14.1. Solution
16.14.2. Services
16.15. Brazil Security Software in Telecom Market Forecast, by Security Type
16.15.1. Network Security
16.15.2. Endpoint Security
16.15.3. Application Security
16.15.4. Cloud Security
16.15.5. Others
16.16. Brazil Security Software in Telecom Market Forecast, by Deployment Type
16.16.1. Cloud-Based
16.16.2. On-Premise
16.17. Brazil Security Software in Telecom Market Forecast, by Applications
16.17.1. Small and Medium Enterprises (SMEs)
16.17.2. Large Enterprises
16.17.3. Government Organizations
16.18. Mexico Security Software in Telecom Market Forecast, by Component
16.18.1. Solution
16.18.2. Services
16.19. Mexico Security Software in Telecom Market Forecast, by Security Type
16.19.1. Network Security
16.19.2. Endpoint Security
16.19.3. Application Security
16.19.4. Cloud Security
16.19.5. Others
16.20. Mexico Security Software in Telecom Market Forecast, by Deployment Type
16.20.1. Cloud-Based
16.20.2. On-Premise
16.21. Mexico Security Software in Telecom Market Forecast, by Applications
16.21.1. Small and Medium Enterprises (SMEs)
16.21.2. Large Enterprises
16.21.3. Government Organizations
16.22. Rest of South America Security Software in Telecom Market Forecast, by Component
16.22.1. Solution
16.22.2. Services
16.23. Rest of South America Security Software in Telecom Market Forecast, by Security Type
16.23.1. Network Security
16.23.2. Endpoint Security
16.23.3. Application Security
16.23.4. Cloud Security
16.23.5. Others
16.24. Rest of South America Security Software in Telecom Market Forecast, by Deployment Type
16.24.1. Cloud-Based
16.24.2. On-Premise
16.25. Rest of South America Security Software in Telecom Market Forecast, by Applications
16.25.1. Small and Medium Enterprises (SMEs)
16.25.2. Large Enterprises
16.25.3. Government Organizations
16.26. South America Security Software in Telecom Market Attractiveness Analysis
16.26.1. By Component
16.26.2. By Security Type
16.26.3. By Deployment Type
16.26.4. By Applications
16.27. PEST Analysis
16.28. Key Trends
16.29. Key Developments
17. Company Profiles
17.1. Market Share Analysis, by Company
17.2. Competition Matrix
17.2.1. Competitive Benchmarking of key players by price, presence, market share, Applications and R&D investment
17.2.2. New Product Launches and Product Enhancements
17.2.3. Market Consolidation
17.2.3.1. M&A by Regions, Investment and Applications
17.2.3.2. M&A Key Players, Forward Integration and Backward
Integration
17.3. Company Profiles: Key Players
17.3.1. Hewlett Packard Enterprise Company
17.3.1.1. Company Overview
17.3.1.2. Financial Overview
17.3.1.3. Portfolio
17.3.1.4. Business Strategy
17.3.1.5. Recent Developments
17.3.1.6. Developing Footprint
17.3.2. IBM Corporation
17.3.3. Accenture PLC
17.3.4. Cisco Systems Inc.
17.3.5. Checkmarx Ltd.
17.3.6. Veracode Inc.
17.3.7. Applause App Quality Inc.
17.3.8. WhiteHat Security
17.3.9. Intertek Group PLC
17.3.10. Symantec
17.3.11. McAfee
17.3.12. Dell EMC
17.3.13. TrendMicro
17.3.14. AVG Technologies
17.3.15. Imperva
17.3.16. Sophos
17.3.17. Check Point (US)
17.3.18. Splunk (US)
17.3.19. Qualys (US)
17.3.20. F-Secure (Finland),
17.3.21. Fortinet (US)
17.3.22. Microsoft Corporation (US)
17.3.23. F5 Networks (US)
18. Primary Key Insights
 To know about the Research Methodology :- Request Free Sample Report
To know about the Research Methodology :- Request Free Sample Report