1. Risk-based Authentication Market Introduction
1.1. Study Assumption and Market Definition
1.2. Scope of the Study
1.3. Executive Summary
2. Global Risk-based Authentication Market: Competitive Landscape
2.1. MMR Competition Matrix
2.2. Competitive Landscape
2.3. Key Players Benchmarking
2.3.1. Company Name
2.3.2. Business Segment
2.3.3. End-user Segment
2.3.4. Revenue (2025)
2.3.5. Company Locations
2.4. Leading Risk-based Authentication Market Companies, by market capitalization
2.5. Market Structure
2.5.1. Market Leaders
2.5.2. Market Followers
2.5.3. Emerging Players
2.6. Mergers and Acquisitions Details
3. Risk-based Authentication Market: Dynamics
3.1. Risk-based Authentication Market Trends by Region
3.1.1. North America Risk-based Authentication Market Trends
3.1.2. Europe Risk-based Authentication Market Trends
3.1.3. Asia Pacific Risk-based Authentication Market Trends
3.1.4. Middle East and Africa Risk-based Authentication Market Trends
3.1.5. South America Risk-based Authentication Market Trends
3.2. Risk-based Authentication Market Dynamics by Region
3.2.1. North America
3.2.1.1. North America Risk-based Authentication Market Drivers
3.2.1.2. North America Risk-based Authentication Market Restraints
3.2.1.3. North America Risk-based Authentication Market Opportunities
3.2.1.4. North America Risk-based Authentication Market Challenges
3.2.2. Europe
3.2.2.1. Europe Risk-based Authentication Market Drivers
3.2.2.2. Europe Risk-based Authentication Market Restraints
3.2.2.3. Europe Risk-based Authentication Market Opportunities
3.2.2.4. Europe Risk-based Authentication Market Challenges
3.2.3. Asia Pacific
3.2.3.1. Asia Pacific Risk-based Authentication Market Drivers
3.2.3.2. Asia Pacific Risk-based Authentication Market Restraints
3.2.3.3. Asia Pacific Risk-based Authentication Market Opportunities
3.2.3.4. Asia Pacific Risk-based Authentication Market Challenges
3.2.4. Middle East and Africa
3.2.4.1. Middle East and Africa Risk-based Authentication Market Drivers
3.2.4.2. Middle East and Africa Risk-based Authentication Market Restraints
3.2.4.3. Middle East and Africa Risk-based Authentication Market Opportunities
3.2.4.4. Middle East and Africa Risk-based Authentication Market Challenges
3.2.5. South America
3.2.5.1. South America Risk-based Authentication Market Drivers
3.2.5.2. South America Risk-based Authentication Market Restraints
3.2.5.3. South America Risk-based Authentication Market Opportunities
3.2.5.4. South America Risk-based Authentication Market Challenges
3.3. PORTER's Five Forces Analysis
3.4. PESTLE Analysis
3.5. Technology Roadmap
3.6. Regulatory Landscape by Region
3.6.1. North America
3.6.2. Europe
3.6.3. Asia Pacific
3.6.4. Middle East and Africa
3.6.5. South America
3.7. Key Opinion Leader Analysis For Risk-based Authentication Industry
3.8. Analysis of Government Schemes and Initiatives For Risk-based Authentication Industry
3.9. Risk-based Authentication Market Trade Analysis
3.10. The Global Pandemic Impact on Risk-based Authentication Market
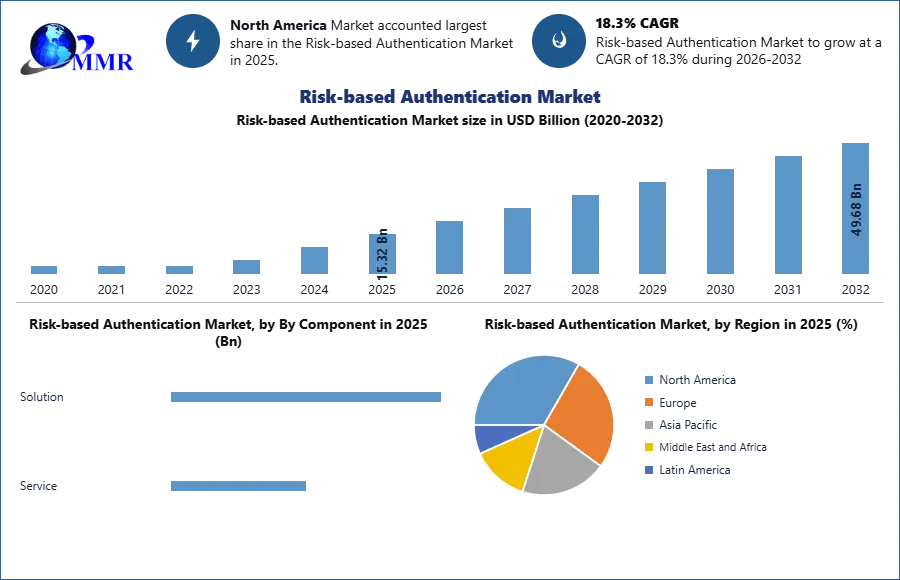
4. Risk-based Authentication Market: Global Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
4.1. Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
4.1.1. Solution
4.1.2. Service
4.2. Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
4.2.1. Multi-Factor Authentication
4.2.2. Behavioral Biometrics
4.2.3. Web Access Management (WAM)
4.3. Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
4.3.1. Cloud
4.3.2. On-premise
4.4. Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
4.4.1. Device-based Policies
4.4.2. Attribute-based Policies
4.4.3. Behavioral Policies
4.4.4. Network and Browser-based Policies
4.5. Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
4.5.1. Banking, Financial Services, and Insurance (BFSI)
4.5.2. Government
4.5.3. Healthcare
4.5.4. Manufacturing
4.5.5. Retail
4.5.6. Telecommunication
4.5.7. Others
4.6. Risk-based Authentication Market Size and Forecast, by Region (2025-2032)
4.6.1. North America
4.6.2. Europe
4.6.3. Asia Pacific
4.6.4. Middle East and Africa
4.6.5. South America
5. North America Risk-based Authentication Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
5.1. North America Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
5.1.1. Solution
5.1.2. Service
5.2. North America Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
5.2.1. Multi-Factor Authentication
5.2.2. Behavioral Biometrics
5.2.3. Web Access Management (WAM)
5.3. North America Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
5.3.1. Cloud
5.3.2. On-premise
5.4. North America Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
5.4.1. Device-based Policies
5.4.2. Attribute-based Policies
5.4.3. Behavioral Policies
5.4.4. Network and Browser-based Policies
5.5. North America Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
5.5.1. Banking, Financial Services, and Insurance (BFSI)
5.5.2. Government
5.5.3. Healthcare
5.5.4. Manufacturing
5.5.5. Retail
5.5.6. Telecommunication
5.5.7. Others
5.6. North America Risk-based Authentication Market Size and Forecast, by Country (2025-2032)
5.6.1. United States
5.6.1.1. United States Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
5.6.1.1.1. Solution
5.6.1.1.2. Service
5.6.1.2. United States Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
5.6.1.2.1. Multi-Factor Authentication
5.6.1.2.2. Behavioral Biometrics
5.6.1.2.3. Web Access Management (WAM)
5.6.1.3. United States Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
5.6.1.3.1. Cloud
5.6.1.3.2. On-premise
5.6.1.4. United States Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
5.6.1.4.1. Device-based Policies
5.6.1.4.2. Attribute-based Policies
5.6.1.4.3. Behavioral Policies
5.6.1.4.4. Network and Browser-based Policies
5.6.1.5. United States Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
5.6.1.5.1. Banking, Financial Services, and Insurance (BFSI)
5.6.1.5.2. Government
5.6.1.5.3. Healthcare
5.6.1.5.4. Manufacturing
5.6.1.5.5. Retail
5.6.1.5.6. Telecommunication
5.6.1.5.7. Others
5.6.2. Canada
5.6.2.1. Canada Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
5.6.2.1.1. Solution
5.6.2.1.2. Service
5.6.2.2. Canada Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
5.6.2.2.1. Multi-Factor Authentication
5.6.2.2.2. Behavioral Biometrics
5.6.2.2.3. Web Access Management (WAM)
5.6.2.3. Canada Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
5.6.2.3.1. Cloud
5.6.2.3.2. On-premise
5.6.2.4. Canada Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
5.6.2.4.1. Device-based Policies
5.6.2.4.2. Attribute-based Policies
5.6.2.4.3. Behavioral Policies
5.6.2.4.4. Network and Browser-based Policies
5.6.2.5. Canada Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
5.6.2.5.1. Banking, Financial Services, and Insurance (BFSI)
5.6.2.5.2. Government
5.6.2.5.3. Healthcare
5.6.2.5.4. Manufacturing
5.6.2.5.5. Retail
5.6.2.5.6. Telecommunication
5.6.2.5.7. Others
5.6.3. Mexico
5.6.3.1. Mexico Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
5.6.3.1.1. Solution
5.6.3.1.2. Service
5.6.3.2. Mexico Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
5.6.3.2.1. Multi-Factor Authentication
5.6.3.2.2. Behavioral Biometrics
5.6.3.2.3. Web Access Management (WAM)
5.6.3.3. Mexico Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
5.6.3.3.1. Cloud
5.6.3.3.2. On-premise
5.6.3.4. Mexico Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
5.6.3.4.1. Device-based Policies
5.6.3.4.2. Attribute-based Policies
5.6.3.4.3. Behavioral Policies
5.6.3.4.4. Network and Browser-based Policies
5.6.3.5. Mexico Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
5.6.3.5.1. Banking, Financial Services, and Insurance (BFSI)
5.6.3.5.2. Government
5.6.3.5.3. Healthcare
5.6.3.5.4. Manufacturing
5.6.3.5.5. Retail
5.6.3.5.6. Telecommunication
5.6.3.5.7. Others
6. Europe Risk-based Authentication Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
6.1. Europe Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.2. Europe Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.3. Europe Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.4. Europe Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.5. Europe Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6. Europe Risk-based Authentication Market Size and Forecast, by Country (2025-2032)
6.6.1. United Kingdom
6.6.1.1. United Kingdom Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.1.2. United Kingdom Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.1.3. United Kingdom Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.1.4. United Kingdom Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.1.5. United Kingdom Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.2. France
6.6.2.1. France Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.2.2. France Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.2.3. France Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.2.4. France Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.2.5. France Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.3. Germany
6.6.3.1. Germany Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.3.2. Germany Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.3.3. Germany Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.3.4. Germany Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.3.5. Germany Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.4. Italy
6.6.4.1. Italy Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.4.2. Italy Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.4.3. Italy Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.4.4. Italy Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.4.5. Italy Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.5. Spain
6.6.5.1. Spain Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.5.2. Spain Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.5.3. Spain Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.5.4. Spain Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.5.5. Spain Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.6. Sweden
6.6.6.1. Sweden Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.6.2. Sweden Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.6.3. Sweden Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.6.4. Sweden Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.6.5. Sweden Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.7. Austria
6.6.7.1. Austria Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.7.2. Austria Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.7.3. Austria Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.7.4. Austria Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.7.5. Austria Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
6.6.8. Rest of Europe
6.6.8.1. Rest of Europe Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
6.6.8.2. Rest of Europe Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
6.6.8.3. Rest of Europe Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
6.6.8.4. Rest of Europe Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
6.6.8.5. Rest of Europe Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7. Asia Pacific Risk-based Authentication Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
7.1. Asia Pacific Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.2. Asia Pacific Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.3. Asia Pacific Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.4. Asia Pacific Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.5. Asia Pacific Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6. Asia Pacific Risk-based Authentication Market Size and Forecast, by Country (2025-2032)
7.6.1. China
7.6.1.1. China Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.1.2. China Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.1.3. China Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.1.4. China Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.1.5. China Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.2. S Korea
7.6.2.1. S Korea Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.2.2. S Korea Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.2.3. S Korea Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.2.4. S Korea Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.2.5. S Korea Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.3. Japan
7.6.3.1. Japan Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.3.2. Japan Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.3.3. Japan Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.3.4. Japan Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.3.5. Japan Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.4. India
7.6.4.1. India Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.4.2. India Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.4.3. India Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.4.4. India Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.4.5. India Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.5. Australia
7.6.5.1. Australia Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.5.2. Australia Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.5.3. Australia Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.5.4. Australia Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.5.5. Australia Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.6. Indonesia
7.6.6.1. Indonesia Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.6.2. Indonesia Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.6.3. Indonesia Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.6.4. Indonesia Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.6.5. Indonesia Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.7. Malaysia
7.6.7.1. Malaysia Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.7.2. Malaysia Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.7.3. Malaysia Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.7.4. Malaysia Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.7.5. Malaysia Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.8. Vietnam
7.6.8.1. Vietnam Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.8.2. Vietnam Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.8.3. Vietnam Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.8.4. Vietnam Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.8.5. Vietnam Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.9. Taiwan
7.6.9.1. Taiwan Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.9.2. Taiwan Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.9.3. Taiwan Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.9.4. Taiwan Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.9.5. Taiwan Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
7.6.10. Rest of Asia Pacific
7.6.10.1. Rest of Asia Pacific Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
7.6.10.2. Rest of Asia Pacific Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
7.6.10.3. Rest of Asia Pacific Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
7.6.10.4. Rest of Asia Pacific Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
7.6.10.5. Rest of Asia Pacific Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
8. Middle East and Africa Risk-based Authentication Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
8.1. Middle East and Africa Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
8.2. Middle East and Africa Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
8.3. Middle East and Africa Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
8.4. Middle East and Africa Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
8.5. Middle East and Africa Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
8.6. Middle East and Africa Risk-based Authentication Market Size and Forecast, by Country (2025-2032)
8.6.1. South Africa
8.6.1.1. South Africa Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
8.6.1.2. South Africa Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
8.6.1.3. South Africa Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
8.6.1.4. South Africa Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
8.6.1.5. South Africa Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
8.6.2. GCC
8.6.2.1. GCC Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
8.6.2.2. GCC Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
8.6.2.3. GCC Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
8.6.2.4. GCC Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
8.6.2.5. GCC Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
8.6.3. Nigeria
8.6.3.1. Nigeria Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
8.6.3.2. Nigeria Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
8.6.3.3. Nigeria Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
8.6.3.4. Nigeria Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
8.6.3.5. Nigeria Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
8.6.4. Rest of ME&A
8.6.4.1. Rest of ME&A Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
8.6.4.2. Rest of ME&A Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
8.6.4.3. Rest of ME&A Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
8.6.4.4. Rest of ME&A Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
8.6.4.5. Rest of ME&A Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
9. South America Risk-based Authentication Market Size and Forecast by Segmentation (in USD Billion) 2025-2032
9.1. South America Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
9.2. South America Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
9.3. South America Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
9.4. South America Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
9.5. South America Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
9.6. South America Risk-based Authentication Market Size and Forecast, by Country (2025-2032)
9.6.1. Brazil
9.6.1.1. Brazil Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
9.6.1.2. Brazil Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
9.6.1.3. Brazil Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
9.6.1.4. Brazil Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
9.6.1.5. Brazil Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
9.6.2. Argentina
9.6.2.1. Argentina Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
9.6.2.2. Argentina Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
9.6.2.3. Argentina Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
9.6.2.4. Argentina Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
9.6.2.5. Argentina Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
9.6.3. Rest Of South America
9.6.3.1. Rest Of South America Risk-based Authentication Market Size and Forecast, by By Component (2025-2032)
9.6.3.2. Rest Of South America Risk-based Authentication Market Size and Forecast, by By Technology Type (2025-2032)
9.6.3.3. Rest Of South America Risk-based Authentication Market Size and Forecast, by By Deployment Mode (2025-2032)
9.6.3.4. Rest Of South America Risk-based Authentication Market Size and Forecast, by By Security Policies (2025-2032)
9.6.3.5. Rest Of South America Risk-based Authentication Market Size and Forecast, by By Industry Vertical (2025-2032)
10. Company Profile: Key Players
10.1. 1. IBM Corporation
10.1.1. Company Overview
10.1.2. Business Portfolio
10.1.3. Financial Overview
10.1.4. SWOT Analysis
10.1.5. Strategic Analysis
10.1.6. Scale of Operation (small, medium, and large)
10.1.7. Details on Partnership
10.1.8. Regulatory Accreditations and Certifications Received by Them
10.1.9. Awards Received by the Firm
10.1.10. Recent Developments
10.2. 2. Microsoft Corporation
10.3. 3. Oracle Corporation
10.4. 4. Cisco Systems
10.6. 5. RSA Security LLC (Dell Technologies)
10.7. 6. Ping Identity Corporation
10.8. 7. Okta
10.9. 8. CyberArk Software Ltd.
10.10. 9. SecureAuth (OneLogin)
10.11. 10. ForgeRock
10.12. 11. Google LLC (Cloud Identity/Context-Aware Access)
10.13. 12. Amazon Web Services (AWS)
10.14. 13. Hewlett Packard Enterprise (HPE)
10.15. 14. Broadcom Inc. (Symantec Enterprise)
10.16. 15. Micro Focus International plc
10.17. 16. Securonix
10.18. 17. Duo Security (Cisco Subsidiary)
10.19. 18. Auth0 (Okta Subsidiary)
10.20. 19. Imprivata
10.21. 20. Thales Group (SafeNet)
10.22. 21. NetIQ (OpenText)
10.23. 22. Entrust Corporation
11. Key Findings
12. Industry Recommendations
13. Risk-based Authentication Market: Research Methodology
14. Terms and Glossary
 To know about the Research Methodology :- Request Free Sample Report
To know about the Research Methodology :- Request Free Sample Report